 Unless you have been living under a rock for the past several months, you probably have heard with alarm about the rising number of data-security breaches. For example:
Unless you have been living under a rock for the past several months, you probably have heard with alarm about the rising number of data-security breaches. For example:2.2 million active-duty personnel in VA data theft - How? An analyst bought home a laptop and external data-drive which was taken during a home burglary.
Not to be outdone by the VA, the Navy somehow let publish personal data of 28,000 service members and their families on a civilian Web site. Navy personnel data exposed on civilian Web site
Feeling left out, the Federal Trade Commission offered up two laptops with data "gathered in law enforcement investigations and included, variously, names, addresses, Social Security numbers, dates of birth, and in some instances, financial account numbers." Bummer. That's gotta hurt someone's pride.
AIG Customers At Risk After File Server Is Stolen - Forget hacking the server, just break in and steal the darn thing! Lost--names, addresses and SSN's.
Laptop theft exposes Hotels.com customer data
Not convinced? Here are more laptop losses, filled with vital data: Laptop Thefts: The Latest Form Of Identity Theft
Like lists? Check out Privacy Rights Clearinghouse's Chronology of Data Breaches Reported Since the ChoicePoint Incident. Deeply disturbing.
I'm convinced we have a serious problem with data security in our country. And I personally think the root of the issue is a little thing called accountability. Accountability means accepting responsibility for something entrusted to you and answering to someone else for any successes and failures in executing that responsibility. It concerns me that confidential data has become so common-place that it is just "data." Let me expound...
I personally really don't think that any of these security breaches were planned by the victims. I really feel that the persons who were entrusted with these laptops and servers took reasonable measures to protect the value of the hardware with which they were entrusted. Few people expect to have their car or home or place of business broken into. Otherwise they would have been prepared ahead of time. Laptops and servers and USB keys and portable drives can be replaced; easily. What they failed to take adequate notice of was the value of the data stored on those devices. Responding to the data loss at the VA alone is costing millions of our tax-payer dollars--not to mention the stress of all those families whose personal data is lost. Maybe the thieves will not be technically savvy and will just delete the data and move on. Maybe not. That's the problem. We don't know.
The VA was offering a reward for the return of the missing equipment. That's another problem. Just because someone turns in the hardware doesn't mean that some clever individual hasn't taken an image (copy) of the data and sold it for an even bigger "reward."
As we gain the ability to data-mine and process even larger amounts of data, we also gain the ability to concentrate that data in larger and larger amounts. The data looses it's individual value (representing a person and life lived) and becomes 1's and 0's joined to a larger set. The people using these databases then relate to the database, not the individuals they represent. Without a face now, it becomes impersonal and accountability shifts from protecting the individual to protecting the trade secrets that database represents to the company or organization. Think about it, just by being a member of our society, your personal information is now contained to some degree in hundreds--maybe thousands of databases--protected only by policies on paper and the willingness of individuals to follow those policies. Feel safe?
I'm not ranting about "big-brother" data-gathering. I'm a jaded child of the digital generation. I expect my surfing habits to be kept in my ISP's logs for years. I expect my banking transactions to be monitored. I expect my telephone calls to be tracked. I don't agree with it all, but neither am I against it all.
So what is the solution? More Federal and State legislation and oversight? Yeah. That always fixes things. No. Instead of working from the top downward, I really think we need to begin demanding more accountibilty from the businesses and government we all work at ourselves.
Why? Because we are our own biggest enemies. One example: a local financial institution hired a security firm to run a pen-test (penetration test) on it's branch. So what's the best way to hack a bank? Get all l33t black-hat hakor on 'em? Nope. They seeded some USB memory sticks with trojans and viruses and left them scattered around where the employees congregated outside the building. Of the 20 they dropped, 15 were plugged into the network's computers and going to town mailing confidential info to the home office. Dirty deeds done dirt cheap. For more info on this trick: Social Engineering, the USB Way
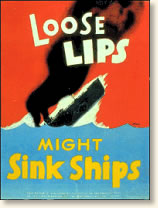 Back during one of our previous "World Wars" the Federal government led a propaganda campaign about the importance of keeping our secrets safe from the "enemy." Maybe you remember the phase "Loose Lips Sink Ships"? My point here is that during a time of national crisis, we worked together to identify and protect information that was critical to our survival; be it military information, personal information, or trade secrets. We understood that information was just as, or even more, important than physical security. I think we need to begin that campaign again. Even if it means the rise of cheesy propaganda posters--updated Flash-style!
Back during one of our previous "World Wars" the Federal government led a propaganda campaign about the importance of keeping our secrets safe from the "enemy." Maybe you remember the phase "Loose Lips Sink Ships"? My point here is that during a time of national crisis, we worked together to identify and protect information that was critical to our survival; be it military information, personal information, or trade secrets. We understood that information was just as, or even more, important than physical security. I think we need to begin that campaign again. Even if it means the rise of cheesy propaganda posters--updated Flash-style!So, until the "Loose Laptops Sink Ships" campaign kicks into gear in the halls of the Pentagon, what's the average Joe Citizen to do? Here are my suggestions--and these can be scaled accordingly from the family laptop level up to the corporate Chief Security Officer's (CSO) desk.
1. Assess your Data: You can't adequately protect what you don't know you have. Run a data-audit on everthing you can store data on: floppy's, CD's, DVD-R's, USB keys, portable/external hard drives (this includes those iPods!), laptops, desktop pc's, and servers. Take a good hard look and sort the information that is confidential (IP tables, personally identifying data, trade and agency secrets, system documentation, etc.) from that which is not (pictures of the family cat, your favorite anime list, etc.). You have to know what you have to assess the impact if it gets lost. Information Security Risk Assessment GAO Practices of Leading Organizations (PDF file)
2. Set a Policy: Who needs access to the sensitive data. Does having your Quicken files on the same pc where your daughter does her IM chat from seem a good idea? Maybe not. Limit what kind of devices can be connected to your pc's/laptops at work (ie, no non-issued USB's). If employees need to utilize data outside the office, consider restricting their acccess to it using VPN accounts directly off the secured servers and not the laptops. Make it difficult to save the data to the local drives. Put the policy in writing. Introduction to Security Policies (a four part series)
3a. Guard the Data--Encryption: This is where it begins to really become work. It doesn't suffice just to have written policy filed in drawer. It has to be implemented. The best way to protect your data is to utilize strong encryption methods. This way, even if the hardware is lost, the data cannot be breached. Windows XP Professional and Windows 2000 that have drives with NTFS filesystem formatting can utilize the optional Encrypted File System (EFS) to encrypt folders and their contents. Apple users can utilize FileVault. Linux users have a wealth of options at their disposal. I personally am using the open source program TrueCrypt. It is very easy to use, is free, and I don't seem to be noticing any performance hits at all (assuming your system has adequate memory, hard drive-throughput speed, and processing power). Leo Laporte and Steve Gibson talk about TrueCrypt here. Too many times users think that just because they have set and use a password to log into their desktop account, then their data is safe. Nope. Not even with NTFS. Just about any hackor or IT professional can probably get to the drive contents using a boot disk/cd and view and copy the files to their heart's content. Heck. I even have tools to let me easily reset the holy "administrator" passwords on Windows machines if somehow a user changes it on me at work. No, the only way to seriously protect data on a drive is to encrypt the data itself, not just depend on a passworded file or operating system.
3(b). Guard the Data--Lock Down Access: This means determining if your location needs to set computer policies that disable use of floppy drives and USB ports via a password protected BIOS. Or maybe you need to implement IP and email monitoring to catch attempts by persons attempting to send files over the Internet or store them on network or other virtual-network drive shares. Yeah it's a hassle when you are issued a company laptop that you can't connect anything to via the USB ports, but that's the point. Do your restrict the use of CD/DVD burners at your location? It just takes a few minutes to burn Gigabytes of data onto a DVD now. Also assess the physical security: do you have a cable-lock for your laptop? Do you avoid leaving the laptop in your car? Do you lock it up even at your residence? Does your server or network room have a hardened door and locks to avoid penetration and theft? What is to prevent a thief from doing a smash-and-grab and walking off with the workstations off the office desks? Lock Down Your PC
4. Track it if Lost: Just because it still got stolen doesn't mean your responsibility has ended. Federal and State laws may require you to notify all the impacted individuals in the case of personal data loss. Your clients might want to know their data is off on vacation. And law-enforcement will always appreciate some leads. There are a number of software and hardware products and services available for tracking down lost equipment. STATE OF THE ART; Making Sure A Laptop Won't Stray
5. Ensure Supporting Software Protection: This seems silly but be sure you are running sufficient network and workstation software protection. This includes anti-virus applications, firewalls, anti-malware scanners (my favorites include LavaSoft's Ad-Aware, Safer Networking's SpyBot Seach & Destroy, Sunbelt Software's CounterSpy, Windows Defender, to name a few), and don't forget about root kit protection (Sysinternal's Rootkit Revealer, F-Secure's BlackLight). These products and others like them help to keep your system protected from data-breaches by malevolent forces.
6. Monitor and Audit it: Make sure you are running periodic inspections to ensure the policies you established are being adhered to. Ask for your employee's devices and audit them for compliance. You can't enforce what you don't know about. Adjust your policy according based on your findings.
7. Don't need it? Destroy it!: Just because you are done with a secure file or hard-drive doesn't mean you should just toss it away. It is getting much easier to recover "deleted" data using any number of freely available tools off the Web. And we are not talking about "Mission Impossible" danger and difficulty levels here. All too often folks have been finding other person's data on drives that were discarded. Couple's Supposedly Destroyed Hard Drive Purchased In Chicago Bummer. There are two products I recommend for secure multi-pass wiping of data prior to disposal: to entirely wipe a drive before disposal I use Darik's Boot and Nuke disk, and for securely deleting individual files and folders in Windows, I use Heidi's Eraser application which integrates into the shell for easy usage. It can also wipe the free-space from drives as well. And that USB key or unused iPod? Wipe those as well or take a hammer to them. Just as effective. Have data tapes, cd's or floppys that you don't need to retain any longer? Drop them into an industrial-grade shredder, or strip the tape, break the CD's and pop the floppy disk out of the case and cut it up.
If we all take personal responsibility in our homes and places of business (be they corporate or government) and hold the persons charged with their safekeeping accountable, then maybe we can begin to put a face on all those loose 1's and 0's out there--after all, it's our face on them.
It's not that the tools and policies aren't there. It just seems--more cases than not--that we aren't following them to begin with. We are failing in our accountability and personal responsibility. Lets get busy and start changing things.
And as for me...I think I'll go apply for a new job over with Public Security Section 9.
Additional Data Security Resources:
U.S. Security Awareness
Security Awareness Program
The Information Assurance Awareness posters
Security Awareness/Motivation Poster Page: Central Coast Security
SecurityFocus website
Laptop Security
Microsoft Shared Computer Toolkit for Windows XP Handbook
Chapter 7: Security Checklist
SANS (SysAdmin, Audit, Network, Security) Institutes's Reading Room
SANS Institute - Popular Resources On Computer Security
NIST Computer Security Division's CSRC Home page
NIST Computer Security Division's CSRC Links and Resources
CERT Coordination Center
That should keep you reading for a while...
06/29/06 Update--Security Guru Bruce Schneier reflects on how economies of cost may be a deciding factor on security policies and implementation efforts. Interesting perspective. It's the Economy, Stupid. Observant commenter Jim Thompson alluded to this as well in his earlier comment here.
See you in the skies,
--Claus
3 comments:
I may be a little off base here...but it seems this issue requires a new paradigm. On one hand, we can continue to rely on those with access to information (read as 80% of the working population) to follow the rules and be disciplined in their use of tech/dbs. On the otherhand, we can challenge those with the tech-savy to propose a new model. IMHO someone has to get WAY outside the box and propose a new model. Ideas?
- digger
I have only skimmed this long write-up, but I believe there's an important principle missing: that of matching your security measures to the value of your data. If you're protecting a $10 million trade secret, your security has to be stronger than if you're just protecting a list of blog passwords or a credit card number. This is something that Bruce Schneier wrote about in one of his recent books: if the cost of breaking your security exceeds the cost of the data being protected, then you're relatively safe. However, if the cost of breaking your security FAR exceeds the cost of the data you're protecting, then you're probably spending to much time, money, and/or effort on your security.
I kinda get more brevity in some of these things.... :)
I completely agree with what you state about security measures matching the value.
I'm mostly soapboxing about the mindset/attitudes of (data) security in general--then trying to add a few positive points to the mix. That we (as a collective/national whole) need to be more sensitive to sensitive data--be it at home or in the workplace.
All too often I come across individuals and groups--both in upper management and the end-users--who express a careless attitude about the value of the data they are entrusted with. I take it personally as I work at a goberment agency and (being the type of guy I am) take it personally as a matter of public accountability and duty. Unfortunately many don't which is why these data-loss events embarrass me.
Data "thieves" go after stuff for lots of reasons, the glory of hacking the challenging target (for bragging rights), for financial gain, for curiosity, for espionage, blackmail, heck, sometimes the opportunity just presents itself and it is just stumbled upon. Remember "War Games?" The kid-character was just auto-dialing for fun and stumbled into that system. I know that is just a movie, but an Agency or Corporation might spend millions a year in external security, but if they let me walk into their offices as a guest, don't have a policy on locking down their pc's and I happen to plug my thumb-drive into an unattended pc while the user is getting me a cup of coffee--who knows what mischief I could walk out the door with, or load onto their system.
I do see the G-Men got their laptop/drive back. They seem convinced that the data wasn't accessed. I hope they can also tell if the drive(s) were imaged or not.....probably not.
Like my bro. posted above, maybe we need to discover a new security paradigm. Where can we effectively maximize protection--knowing human nature like we do...in the gatekeepers and their systems or in the gates themselves? Or are we all responsible to step up and use the gates we have already designed and take our turn on the guard-watch.
It all starts with awareness of the problem.
Post a Comment