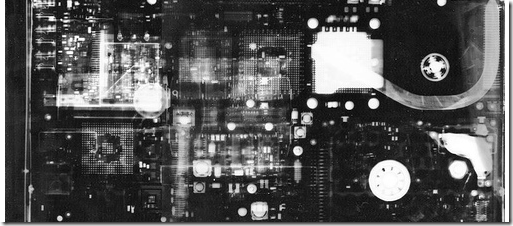
cc attribution “thinkpadx32 under X ray” by jeroyang
I’ve been holding onto this pile for quite a while and it has come time to release it into the wild.
These are all the major Windows process tools and utilities I have come across and used from time to time.
Besides the first two sets, the rest really aren’t listed in any particular order or ranking.
Please note there are some great CLI-based tools as well but those will have to wait. We are focusing on GUI tools for now.
Of course, there is still the Windows Ctrl-Alt-Del “Task Manager” but except all but the average users, it just doesn’t have the horsepower to cut it in exploring, understanding, and manipulating running processes. I think of it as the training wheels of a kiddo’s bike. Once you’ve gotten used to it, time to take it off and graduate to the real-deal.
Crème-of-the-Crop
These (IMHO) are simply the best of the class. With practice, familiarity, and repeated usage it’s hard to turn to any other tool.
- Process Explorer – Microsoft Sysinternals. Simply the best. Nothing else to say.
- SystemExplorer – Actively updated, this program provides more muscle that the standard task-manager, but presents the information in a user-friendly way.
- Free Extended Task Manager – The tabbed interface is nice and makes browsing between features pretty simple. Very similar in style to the default task-manager application, should be good enough for most users.
Style is the Thing
Not to say that these alternative process explorers don’t also have substance, but each seems to deliver the basic Windows process management tools in different GUI formats. You might find some features special to a particular application but overall, if you find one you are comfortable with using, awesome. Stick with it.
- Security Process Explorer.
- Process And Port Analyzer 2.0 - real time process, port and network connections analyzer. Download link via Softpedia.
- AnVir Task Manager Free.
- MKN TaskExplorer 5. For more information see this Better Windows task management with MKN TaskExplorer post over at Download Squad
- Yet Another Process Monitor (YAPM) – cute and neat tool. CyberNet had a good review of the utility in their YAPM: Process Manager with a Ribbon UI post.
- Accueil – Bill2’s Process Manager. Yep. Site in French. (screenshots.) Just download, unpack and switch the language to English and you should be set. Lots of nice features in a well designed GUI. See this ghacks review post of the tool for more information to get started with.
- Process Hacker – Another nice tool but be aware that it does require .NET 2.0 or higher to run, and that while supporting x32 and x64 bit systems, some features only enabled in x32 OS versions.
Targeted Process-Related Tools
I think of these as specialized tools that interact and support the Windows process tools listed above. When coupled with the information that the “standard” process explorer tool provides, these supplement that information when hunting down malware or studying the extended behavior of a running process.
- Process Monitor – Microsoft Sysinternals. Goes hand-in-hand with Process Explorer. Great logging tool when tracing just what activity a process does on your system.
- OpenedFilesView – Nirsoft - View opened/locked files in your system and the processes that control them.
- mst IsUsedBy – mst software – another tool to see what has opened a particular file on your system.
- ProcessActivityView – Nirsoft - Show file activity summary/logging for a specific selected process. Unlike Process Monitor that captures everything and then you filter for what you want, PAV is used to select a specific process and log activity for that process. Particularly useful when logging program installation processes to see what and where they install stuff to.
- CurrPorts – Nirsoft – shows what ports all the running processes have open. Really useful. Updated often and in both x32 and x64 versions for Windows. The cat’s meow.
- VStat - Robin Keir – Similar to CurrPorts and my preferred tool (only from a GUI perspective) for port monitoring of processes on XP systems at work. Nir’s CurrPorts is still a bit better, however.
- TCPView for Windows – Microsoft Sysinternals – I don’t use this one often anymore since finding CurrPorts and VStat but hey, it’s Sysinternals.
- WinLister – Nirsoft - Display the list of opened windows on your system for matching up processes to displayed windows.
- Window Seizer – Alex Nolan – GUI-rich tool for matching and manipulating the location of windows. I use this when I have undocked my laptop from the secondary monitor and then when I launch and app and it appears on the “phantom” 2ndary monitor, I hit the “Move to 1,1” button to bring it back to my visible monitor surface.
- WinPatrol 2010 (Free) and WinPatrol ToGo- Bill Pytlovany – See also the fantastic tool ($) WinPatrol 2010 Plus. All great tools for keeping an eye on and controlling processes on your system (and then some!).
- ScTagQuery. This is some CLI stuff but was too good not to include. From the developer’s description “ScTagQuery allows you to obtain precise information on which threads in the system are being used by what service, in order to better gauge CPU and resource usage as well as to help in debugging service-related problems. ScTagQuery can be used to map service tags to a service either on a live system, or by running the tool on the same system as where a crash dump occurred, since service tags remain the same after reboot. Apart from mapping service tags to services, and querying the service tag for a thread, ScTagQuery can also show system-wide tag information, as well as dump the name of each service associated to any thread on the system.” for more info see this blog post by the developer: ScTagQuery: Mapping Service Hosting Threads With Their Owner Service
- MemInfo. Again another CLI tool and memory specific, but does have some nifty tie-ins to processes. “MemInfo is a tool to query information on the state of the memory manager page lists, page frame number (PFN) database entries, per-component and per-process memory usage, and for mapping virtual to physical addresses (for certain kinds of kernel-mode pointers). It can also display the physical memory ranges available for use by Windows and reported by the BIOS and/or ACPI tables. MemInfo can help detect bad or damaged memory sticks by displaying the size of the bad page list, as well as help in detecting certain kinds of malware or rootkits by showing processes that tools other than the kernel debugger may not show as present. It can also be used to diagnose certain situations where the number of memory available to Windows is different from the amount of memory installed on the system.” More info? See the blogpost MemInfo: Peer Inside Memory Manager Behavior on Windows Vista and Server 2008
- Svchost Process Analyzer – Tool to focus specifically on the mysterious Svchost processes - a svchost.exe file checker. “The free Svchost Process Analyzer lists all svchost instances and checks the services they contain.”
Incident Response Specific Process Tools
While these tools are specifically geared towards the incident responder and forensics dude/dudettes, sysadmins could find they provide a particular level of process and/or static file capture and analysis that the aforementioned tools don’t natively provide. They might help with sorting of initial data on processes.
- MANDIANT’s Red Curtain – Quoting…”MANDIANT Red Curtain is free software for Incident Responders that assists with the analysis of malware. MRC examines executable files (e.g., .exe, .dll, and so on) to determine how suspicious they are based on a set of criteria. It examines multiple aspects of an executable, looking at things such as the entropy (in other words, randomness), indications of packing, compiler and packing signatures, the presence of digital signatures, and other characteristics to generate a threat "score." This score can be used to identify whether a set of files is worthy of further investigation.”
- MANDIANT Memoryze. No other good way to describe it so here it is direct from Mandiant’s product page:
MANDIANT Memoryze is free memory forensic software that helps incident responders find evil in live memory. Memoryze can acquire and/or analyze memory images, and on live systems can include the paging file in its analysis.
MANDIANT Memoryze can:
- image the full range of system memory (not reliant on API calls).
- image a process’ entire address space to disk. This includes a process’ loaded DLLs, EXEs, heaps, and stacks.
- image a specified driver or all drivers loaded in memory to disk.
- enumerate all running processes (including those hidden by rootkits). For each process, Memoryze can:
- report all open handles in a process (for example, all files, registry keys, etc.).
- list the virtual address space of a given process including:
- displaying all loaded DLLs.
- displaying all allocated portions of the heap and execution stack.
- list all network sockets that the process has open, including any hidden by rootkits.
- output all strings in memory on a per process basis.
- identify all drivers loaded in memory, including those hidden by rootkits.
- report device and driver layering, which can be used to intercept network packets, keystrokes and file activity.
- identify all loaded kernel modules by walking a linked list.
- identify hooks (often used by rootkits) in the System Call Table, the Interrupt Descriptor Tables (IDTs), and driver function tables (IRP tables).
MANDIANT Memoryze can perform all these functions on live system memory or memory image files – whether they were acquired by Memoryze or other memory acquisition tools.
- Nigilant32
Nigilant32 is an incident response tool designed to capture as much information as possible from a running system with the smallest potential impact. Nigilant32 has been developed with Windows 2000, XP, and 2003 in mind, and should work fine with computers running one of those operating systems. Nigilant32 is beta software and may not work in all instances.
* Nigilant32 For First Responders: The SnapShot,Using Nigilant32 we can review and save a report of the running system that includes Processes, Services, User accounts, Scheduled Tasks, Network Ports, etc.
It can also perform sector viewing and memory imaging.
- NTCore - Explorer Suite and PE Detective – really designed for hard-core programmers and PE analysts. It does have some tools to help explore processes associated with executables.
- ESET SysInspector - “ESET SysInspector is a free, state of the art diagnostic tool for Windows systems. It is also an integral part of ESET Smart Security 4 and ESET NOD32 Antivirus 4. It peers into your operating system and captures details such as running processes, registry content, startup items and network connections.” From there it performs heuristic analysis on the processes and reports them. This can help narrow your examination. More in this older GSD post SysInspector: New System Utility from ESET
Mostly Process Manipulation Tools
These additional tools are really, really targeted for working with and manipulating running Windows processes. Best left to the folks who know what they are doing. Can do some really cool things, but also bork-things-out bad if not done correctly.
- Daphne – Tool to kill, control, and debug processes. No-frills GUI. See this Download Squad post for more info as well as this Daphne Process Explorer 1.37 PortableApps beta version.
- Seem - System Eyes and Ears Monitor – Multi-purpose tool that includes process exploration along with other disk and rootkit hunting features.
- Prio - Priority Saver – Process priority level manipulator. Process Explorer (and others) also do this, but this is a specific tool for that task. Particularly valuable if you need to “permanently” set the priority to work that way at launch each time. See also this GSD post Windows CPU throttling techniques for lots more, including Process Lasso
- PMW (Process Manager For Windows) – Interesting as this tool adds process priority controls to the right-click menu for the running process item.
- Home Page: Spy++. Spy++ (SPYXX.exe) was a Microsoft tool that “…that gives you a graphical view of the system’s processes, threads, windows, and window messages.” Unfortunately it is really hard to find nowdays.
- ManagedSpy – appears to be the replacement tool for Spy++. “ManagedSpy displays managed controls, properties, and events. ManagedSpyLib allows you to programmatically access Windows® Forms controls in another process. You can get and set properties and sync on events in your own code. ManagedSpyLib can also help you build test harnesses and can perform window, message, and event logging.” Really for programmers and debuggers, it can sometimes extract useful info for process and executable analysis.
- Increase Windows Stability via ghacks notes the tool xTra Windows Stability which offers to control and manage processes. Appears XP specific and I haven’t messed with it on Vista/Win7. There was a comment in the page from Kris that says:
- RunScanner – Sort of rolls up a variety of startup/process capture tools into one. Useful for troubleshooting a malware infected system with a non-technical end-user.
- Alin Constantin's WinCheat – Another process and debugging tool of sorts loaded with special sauces.
This will just modify three registry keys – you might as well just use the .reg file rather than a program dedicated to it.
Windows Registry Editor Version 5.00
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer]
“DesktopProcess”=dword:00000001[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced]
“SeparateProcess”=dword:00000001[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\BrowseNewProcess]
“BrowseNewProcess”=”Yes”(note that the .reg file needs to be saved with ANSI encoding for Windows to recognise it).
I have put a copy here for your convenience:
http://a.nfshost.com/separate_processes.reg
* Pick visible windows with the mouse and see information about them (like MsSpy++ does, but identifying better the window usnder the cursor).
* Explore the windows hierarchy of the current desktop.
* Allow to see and modify windows styles
* Send/post messages to windows, enable/disable/show/hide them
* Capture the text from windows (and yes, this works for password fields on WinNT/Win2000/WinXP)
* Capture/save window content as bitmap
* Magnify a rectangle on screen following the mouse movements
Related Posts
- System Process Tools – Grand Stream Dreams Blog.
- 3 Tools To Manage Windows Processes Better - MakeUseOf.com.
- Five Best Windows Task Manager Alternatives - Lifehacker.
- I will kill thee a hundred and fifty ways...freely – Grand Stream Dreams Blog..
Enjoy!
--Claus V.
No comments:
Post a Comment