I just couldn’t wrap up the weekend without sharing these links. I’m so going to be nodding off in my training class tomorrow. Must bring Thermos of extra coffee with me! Don’t want to make the teacher unhappy!
So many network tools, tricks, and nuggets came out last week I’m still exciting thinking about how to use them all!
Security Advisory: Two Vulnerabilities in NetworkMiner - NETRESEC Blog - Don’t let the boring post title fool you! Based on this, Erik Hjelmvik has released a new version of NetworkMiner! Now sparkling at version 1.5 (free/pro editions)
NetworkMiner packet analyzer - Download NetworkMiner version 1.5 (free) here.
While I was doing some super-fast (but apparently productive) beta testing for Erik on some Windows 7 and Windows 8/8.1 systems, I noticed I wasn’t getting great results from my test captures made with and being processed in NetworkMiner. My “doh”. Erik kindly reminded me of his post NETRESEC RawCap - A raw socket sniffer for Windows where he pointed out that using Windows raw socket sniffing has some problems. I had forgotten I didn’t yet install Wireshark/WinPcap on these particular test systems. From Erick’s post:
Microsoft's newer operating systems (later than WinXP) have limitations associated with raw socket sniffing of external interfaces, i.e. everything that isn't localhost. Known limitations in Windows Vista and Win7 are:
Due to these limitations in the raw sockets implementations of Microsoft's current operating systems we suggest running RawCap on Windows XP if you need to capture from external interfaces.
- Windows 7 - Can't capture incoming packets
- Windows Vista - Can't capture outgoing packets
Baselining Dropbox With Wireshark (by Tony Fortunato) - LoveMyTool blog video presentation.
Editing Tracefiles With TraceWrangler (by Tony Fortunato) - LoveMyTool blog video presentation. This short video presentation on a new (Alpha release) tool, TraceWranger blew me away. There are methods of sanitizing trace files for sharing/training but they are fraught with challenges for mere mortals. This new tool is amazing and I really hope the developer Jasper Bongertz gets the support needed to encourage his continued refinement and development of this valuable tool for analysts.
- TraceWrangler - (alpha software) - currently at build version 0.1.3. Standalone application. No installation needed. Unzip and go. Written by Jasper Bongertz.
- TraceWrangler Documentation - This is Must Read material if you are interested in using this tool properly
- Starting TraceWrangler - the basics
- Anonymization Tasks - details for the options
- Trace File Sanitization NG - SEC-04_Trace-File-Sanitization-NG_Jasper-Bongertz (PDF) - Link to his presentation of the tool at Sharkfest 2013.
- Sharkfest 2013 - Trace File Sanitization (Jasper Bongertz) - YouTube. While PDF versions of presentations are nice, on a whim I decided to see if Jasper’s presentation was actually up on YouTube for viewing. It was!
- Trace file sanitization for network analysts - Packet Foo - Jasper’s blog post with additional details on his tool in case you missed the presentation.
- The notorious Wireshark “Out of Memory” problem - Packet Foo. Oh how this has hobbled me over the years! So much so that CLI based captures became my dearest friend!
- Packet Foo RSS - Yeah. It’s that good. Feed yourself on it!
Nmap - Now at version 6.40 - Free Security Scanner For Network Exploration & Security Audits.
- Nmap Change Log
- Download Nmap Security Scanner - for Linux/MAC/UNIX or Windows
Message Analyzer Beta3 Refresh has Been Released (Build 6215) - MessageAnalyzer - Lost in all the news was a quiet announcement of the next generation of Microsoft’s own network traffic analysis tool MessageAnalyzer getting a Beta 3 refresh release. The interface is very different (to me) from Wireshark, but since I used NetMon a ton to supplement my Wireshark work, it is taking some getting used to.
HolisticInfoSec: toolsmith: C3CM Part 1 – Nfsight with Nfdump and Nfsen - HolisticInfoSec blog - Russ McRee’s post rocks on so many levels. Well worth the read and review.
Firefox Developer Tool Features for Firefox 23 - Mozilla Hacks – the Web developer blog. In case you missed it, Firefox 23 was released last week. Included in it (besides the new app icon update) was a new network tool called “Network Monitor.”
I so love this! “F12” is the new “must know” hotkey in these modern browsers!
If only Mozilla (or Chrome or IE 10) were “approved” web-browsers in our enterprise. This feature alone would so help with network and web-app diagnostics and troubleshooting from the end-user desktops.
What’s that you say? One single element of your cloud-based web-application seems to time out in IE 8, crashing your session? The network is fine, site bandwidth is fine. Your PC is fine. Seems like it could be a server-side application issue. Let me make a ticket for your issue and send it up. (Response often comes back, “There is no problem…must be a client-side issue…check the PC and bandwidth, follow our response template and let us know…”) (Sigh…)
- Network Monitor, now in Firefox Beta - Mozilla Hacks – the Web developer blog - More details on the feature.
- A look at Firefox's new Network Monitor - Ghacks - Martin Brinkmann does an outstanding job introducing it as well.
Turns out Chrome web browser can do this trick as well
- Evaluating network performance - Chrome DevTools — Google Developers
- Performance profiling with the Timeline - Chrome DevTools — Google Developers
- Chrome Dev Tools: Networking and the Console - Nettuts+
- Google Chrome Dev Tools: Network Panel - TechRepublic
Turns out that Internet Explorer (IE9, IE10, IE11) also have a “F12” feature for network analysis in the browser.
- Introduction to F12 Developer Tools (Windows) - IE Dev Center
- Navigating the F12 Developer Tools Interface (Internet Explorer) - IE Dev Center
- Internet Explorer's F12 Developers Tools: A feature walk-through - TechRepublic
- A Peek at Internet Explorer’s Developer Tools - Nettuts+
- Network Traffic Capturing with IE9 Developer Tools - LINQED.NET
And in IE11, it’s about to bring the house down on the competition!
Debugging and Tuning Web Sites and Apps with F12 Developer Tools in IE11- IEBlog. OMG!!! I am so crushing on the new “F12” profiling and responsiveness tool interface in IE 11! Please tell me this is going to be backwards compatible with Win 7. (Why yes, Virginia, it is…)
Anyway, back to more Firefox 23 release news and details.
- Firefox 23 lands with a new logo and mixed content blocking - Ars Technica
- Firefox Notes - Desktop - Mozilla.org
- Firefox 23 enables mixed content blocking, consolidates search settings - BetaNews
- A Look At What's New In Firefox 23 - Addictive Tips blog
Troubleshooting TCP/IP Connectivity Issues with This Command-Line Utility Portqry.exe - Next of Windows. Been using portqry.exe from the command line along with the PortQueryUI GUI fro some time. Dead helpful in a pinch!
PuTTY: a free telnet/ssh client - just released at version beta 0.63 for you console fans! See the extensive Changes page for all the details
- PuTTY Portable 0.63 - PortableApps.com build version as well is available and updated.
KiTTY - let’s not forget about this fork version of PuTTY that has some additional bells-and-whistles!
- News - latest KiTTY news is update 0.62.2.3 minor update in late May 2013.
- Recent changes - tracking site-changes at KiTTY’s house
- KiTTY Portable - why “yes” there is a PortableApps.com build version as well for KiTTY fans.
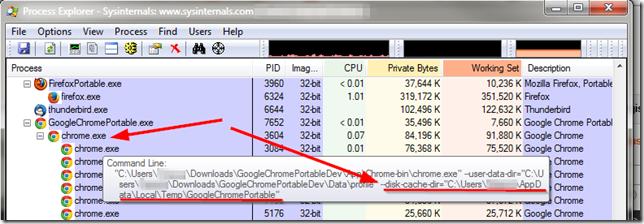
Finally, at home I run Mozilla Firefox, Portable Edition and Google Chrome Portable rather than installing them directly on my system. However I was trying to use some of NirSoft’s Browser Tools to explore and check my Google Chrome(ium) cache and wasn’t finding anything at all.
Strange. Bug in the tool?
Turns out the answer was “of course not dummy” it’s the dummy’s bug.
Where is the Google Chrome Portable cache folder? - PortableApps.com. Bruce Pascoe kindly puts it like this:
Chrome Portable, like FFP, doesn't save the cache by default.
Note that unlike Firefox however, there's no way to turn the cache off completely in Chrome, so while it's running the cache is stored in the local temp directory (%TEMP%), but then it's immediately deleted when you exit Chrome.
So anyway, yeah, no surprise that you couldn't find it.
and cleared up a bit by “The MAZZTer”
The cache folder is saved in %TEMP%\GoogleChromePortable.
Where the %TEMP% is the user’s temporary file location under their profile.
This is interesting as it explains why the NirSoft tool ChromeCacheView wasn’t finding anything while pointing to the default user profile location in my Portable Apps application structure that ChromeHistoryView didn’t seem to have any issue with parsing. So even though the files were removed when the program terminated, it most likely did not “secure” delete them, so (depending on overwrite activity of the file system/free-space scrubber utilities) it might be possible to carve and recover them from a system that the portable-apps version of Chrome was used on. And that sounds like a challenge for another day…
Cheers!
--Claus Valca

1 comment:
Opera has it too. Its part of Opera Dragonfly...this is Opera 12 and previous ones. The latest one (15) is still just a chrome clone at the moment as they add in more features.
Post a Comment