Public domain photo: taken by U.S. Air Force Senior Airman Julianne Showalter
Anti-Malware news
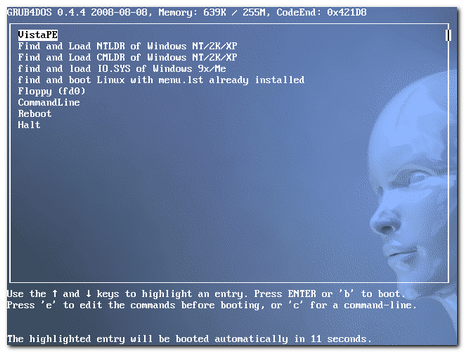
- VIPRE PC Rescue - (freeware) - Sunbelt Software is now offering a “standalone” anti-malware scanning/removal tool. The self-extracting executable is updated daily with the latest signatures. Scans include rootkit detection. “Four command line options are available, enabling the program to perform a boot scan during the next start-up, perform a deep scan, log the events, and disabling the rootkit.” I really like the fact that not only can you download and execute it from the net, but you can keep it packed/unpacked on a USB stick and run from there. I’ve been using the full VIPRE product from Sunbelt Software for a while now and am very impressed with it. A full GSD review on both should be coming soon. Sunbelt reports that they will be providing a guide on how to use VIPRE PC Rescue with a bootCD for non-bootable system use. Sounds like a great add-on for VistaPE or other WinPE based boot disks. Spotted via the Sunbelt Blog.
- Portable Anti-Virus/Malware Security Tools: A Primer – earlier (related) Grand Stream Dreams post. Looks like I am going to have to do an updated post to add VIPRE PC Rescue to it. If you haven’t seen that post back and you liked the VIPRE PC Rescue product, visit that one to snag some more soldiers for your battles.
- A bit of VIPRE roadmap – Sunbelt Blog. I’m really pleased with VIPRE and the performance it offers across our home systems. It is easy to use and the girls never ask me questions about what it is doing. Alex’s crack development team is hard at work making it even better. Not only is the core detection engine about to be upgraded, but it will also include a feature called MX-Virtualization technology (MX-V). As Alex explains it, MX-V will provide “…an extremely compact virtualized Windows environment to test for the presence of malware.”
In the MX-V system, malware is executed in a virtual Windows environment that mimics many of the core Windows functions -- registry, file system, internet connection, mouse clicks, etc. The actions of the malware are then analyzed for behavioral characteristics common to malware, or to look for certain malware signatures. By analyzing malware in this fashion, VIPRE is able to detect many types of malware without the necessity of creating a constant stream of dedicated unpackers and signatures for each variant of a piece of malware.
- Spybot-S&D – v1.6.2 Released - (freeware) – Granted, I rarely turn to this tool much anymore. With VIPRE running, and the other portable anti-malware tools and other anti-malware tools and core Windows system utilities at my disposal, I have more options than ever before. However it is hard to leave it behind and I keep it updated anyway. According to the post this latest version now includes support for “…the latest Opera releases, support for Googles new browser Chrome, fixed support for fresh older Firefox installations, improved support for fast user switching while Spybot is running, plus a few more bugfixes.” Tantalizingly, they also mention that a preview release of Spybot S&D 2.0 will be available soon. No link to download just yet but fans of Spybot S&D can drool over these Spybot 2.0 alpha screenshots buried in their official forum.
- Ad-Aware Free Anniversary Edition 8.0 - (freeware) – This latest version looks even more 2.0 in the GUI. To be honest, I haven’t used Ad-Aware for a very long time (ever since the SE version got dumped and it failed to be able to be run off a USB stick). This version claims improved performance and tweaks, rootkit removal support, and integration with Windows Security Center for what its worth.
- hype-free: Can you test AV using VirusTotal? – cdman83’s thoughtful blog post on the merits of VirusTotal and a lively follow-on comments discussion. Basically, I think it comes down to understanding that these on-line scan services act as a line to examine an unknown suspect file to see if if contains or exhibits malicious code. It is not a test or comparison of the performance (efficacy) of some AV/AM products over others. At least that’s how I’ve always looked at it. Keep these services in context and use them as a first-response tool to examine a suspect executable/file. Understand the limitations and that just because a submitted sample passes/fails, doesn’t necessarily mean anything. It is just data to be used as part of a skilled responder’s analysis of the file and possible threat. As cdman83’s comments and supporting links indicate, having a accurate understanding of their strengths and weaknesses leads should lead to more realistic usage and results interpretations.
Drive Encryption and Authentication
- Caviar 2TB – When I first got my 500GB HDD for our desktop system, I thought, geez. That’s too much. Now, with a price-point of about $299, I’m wondering how I can get one for our home. It’s SATA so I couldn’t (easily) use it on my current system, but a future system upgrade might provide a home. Holy Hopscotch! 2TB. I’m trying to get my mind around that. I don’t yet find any TB-level drives for laptops just yet. These Newegg offered 500GB drives are the closest. Yet at about a $100 price-point, they also seem too good to pass on.
- Hard drive manufacturers back new disk encryption standard - Ars Technica. Instead of a software-based HDD solution, drive manufactures are attempting to deal with it at a firmware level. Ars points out that while drive encryption does provide data protection, it does not solve the issue with hardware protection and while data might be safe, the drive could be possibly be reformatted or replaced (at minimal cost). And these only protect systems/data at rest. As we have seen, hackers can successfully intercept unencrypted data one the disk-encryption has been decoded after successful boot with rootkits, trojans, data-sniffers, etc. As we are finding out ourselves at work, Whole Disk Encryption also poses challenges for IT system support. It’s hard to remote-boot/access a WDE system. Use of tokens or a common administrator access code lowers the security the system is supposed to protect. With WDE we are unable (kinda) to OS boot a system to perform any form of on or off-line service and troubleshooting unless we use a token that erases the user’s code (then they have to pick a new one) or ask the user to give us theirs to use. At least it’s a start in the right direction.
- Binary Intelligence: Encrypted Drive Standard – links to the official standards.
- CYB3RCRIM3: Authentication and the Erased Hard Drive – Interesting legal case where the defendant requested provision of the police investigation’s hard-drive (for the system used to communicate with the defendant in on-line chat sessions)…which ended up getting erased, thus according to the defendant, prevented his defense in attempting to authenticate/disprove the official record/logs provided against him by law enforcement. Computer forensic experts are all over handling the suspect drive with duplication and chain of custody control. But it raises a question to this layperson…is the same process handled when a law-enforcement drive is used during an investigation? Anyone care to comment?
- End to End Encryption is NOT the PCI Silver Bullet! - Branden Williams’ Security Convergence Blog – Wonderful perspective. Yes, the Heartland credit processor appears to have been victimized by malware code lurking in the unallocated file space. Yes, whole drive encryption, and encryption of PCI data while transmitted helps. But even at some basic level, critical data must be unencrypted to be used by the system or system points. Those will always be the chinks in the armor. Constant Vigilance! as Mad-Eye Moody might say is probably the only solution.
- Going back to the whole disk encryption thought, don’t forget that there are (at least) two long-running free programs that you might consider looking into; CompuSec and TrueCrypt. It will at least keep your data safe in the event of system theft.
Mostly Forensics
- Free SANS Forensic Training for Local Law Enforcement - SANS Computer Forensics, Investigation, and Response blog – SANS forensics course program allows federal law enforcement officers who sign up for the class to bring along a local law enforcement officer with them for a free training “ride-along". That’s neat!
- Forensic Incident Response: Using RegRipper – Hogfly offers up some additional applications for using Harlan’s great Regripper tool. System Admins take note.
- Windows Incident Response: Catching up... – Harlan has been hard at work on finishing the next edition of his computer forensics book. However, this post shows that he has still managed to keep a close on on great sources of forensics information and developments in the field. All great links.
- Ascension Blog » Digital Forensics – Links to a paper by Ian Charters directed towards “..the laymen and explores how digital forensics has evolved over the years.” Neither deep or technical, it does provide a nice overview on digital forensics and the issues the field has gone through.
- Dates from Unallocated Space - « SANS Computer Forensics, Investigation, and Response – short but interesting piece. Useful not just for forensics crowd but also for system administrators working on a system.
Security Stuff
- Heartland Sniffer Hid In Unallocated Portion Of Disk – gcisecurity blog – more details on how Heartland got hacked.
- Conficker/Downadup Scanning – SANS ISC Handler’s Diary post about network scanning characteristics of this baddie.
- TinyURL Security Issues Revealed – InfoSecurity blog and Finjan MCRC Blog 2009 - Evasive URL techniques – Turns out that use of a “tinyURL” link often will cause bypass of many web-based “safe-browsing” url link scanners. Yet another reason to beware of these links without checking them out first. I’m still waiting for a Firefox 3.x version compatible release of Long URL Please.
- IT Security Expert: Monster Jan09 breach: The Website Passwords Problem – Oh my. Dave Whitelegg goes to task on Monster for numerous problems with their security model. If you have a Monster.com account or deal with website security, it’s a good read.
- Monster.com - They Just Don’ Get It! | Infosec Ramblings – Kevin picks up on Monster’s beatdown where Dave left off. Where is the SSL encryption? Not anywhere Dave can find!
- Test your defenses against malicious USB flash drives - Computerworld Blogs – Long and detailed discussion of issues related to USB devices. We’ve already covered it a lot at GSD before here and again here, but this is another great reminder and perspective.
- New Tool: wlan2eth – New find for the network security folks from Josh Wright:
- VRT: Dial-up Security woes in East Africa - Alain Zidouemba goes on a trip to visit family in East Africa and finds that pervasive use of dial-up Internet access brings headaches. Couple that with plans that are minute-based, big DAT files and security patch updates from vendors often discourage security updating of software and systems. In a growing consumer broadband centric world, what options exist for keeping these folks and systems safe and current? Yes, I know folks can use a variety of off-line system patching solutions, all are great, but unless you still have access to a broadband connection or friend with one, systems for these users often end up being on the front-line of computer security battles, and cannon-fodder. The post is a good read.
“Wlan2eth is a simple tool to convert packet captures in 802.11 format to Ethernet format. Lots of tools can only understand Ethernet link types, so I wrote this tool to convert captures to a format that they can understand.
“For each packet in an input 802.11 capture file, wlan2eth examines header values to ensure it is a data frame, then it creates a new output packet with an appropriate Ethernet header (source and destination address and embedded protocol field are preserved from the 802.11/802.2 header). Timestamps are also preserved from the original capture.
“This tool is really only useful for encrypted traffic, though you could use it with a tool such as airdecap-ng to decrypt an encrypted capture first, then convert the unencrypted output file to Ethernet format.”
Keep Safe.
--Claus V.